The Association of Independent Data Auditors of India (AIDAI) has organised a webinar to introduce the concept of Independent Data Auditors to professionals particularly not presently identified as Privacy Auditors.
The webinar is scheduled for May 23rd 11.00 am.
 The Registration link is available here:
The Registration link is available here:
https://us02web.zoom.us/j/88286391275?pwd=wrP6fgGrCWTOVPv9p53RFvo22JgeJo.1
A request sent by the Secretary AIDAI is reproduced below:
Dear Professional Friends,
We are delighted to inform you that the ASSOCIATION OF INDEPENDENT DATA AUDITORS OF INDIA (AIDAI), was established in April 2026 as a pioneering new vertical of FOUNDATION OF DATA PROTECTION PROFESSIONALS IN INDIA (FDPPI).
This initiative marks a significant milestone in India’s evolving data protection and digital governance landscape, arriving at a time when organisations across sectors are preparing to align themselves with the transformative framework introduced under the Digital Personal Data Protection (DPDP) Regime.
AIDAI has been conceived as a forward-looking professional platform dedicated to building a credible ecosystem of INDEPENDENT DATA AUDITORS (IDA) capable of supporting organisations in achieving robust privacy and compliance standards. The platform creates a unique and timely professional pathway for experienced CAs, ICMAs, CS, Legal, GST practitioners and similarly placed professionals, and Governance practitioners, presently in auditing field, to expand their expertise into the rapidly emerging domain of Data Protection Auditing and Privacy Compliance Services. For more information, please listen to YouTube presentations @
https://www.youtube.com/watch?v=_p2JWVG47Qk and
https://www.youtube.com/watch?v=B4MF_RdCAX4&t=390s
As you are aware FDPPI is a Section 8 non-profit organisation driven by a nationwide network of distinguished Data Protection and Privacy professionals under the able leadership of Vijayashankar Nagaraja Rao, popularly known as Naavi, a pioneer in the field of Cyber Laws in India. With a vibrant membership base of over 500 professionals across India, FDPPI has consistently worked towards promoting awareness, capacity building, professional excellence, and responsible data governance practices in the country.
Now AIDAI aims to expand privacy-compliance services by formally empanelling qualified professionals to perform DATA PROTECTION AUDITS, ASSESSMENTS, AND ADVISORY SERVICES for businesses seeking compliance under DPDPA 2023, DPDP Rules 2025, and related frameworks. Here are 3 different Empanelment categories of IDA’s and their benefits
1) Probationary Independent Data Auditor (PIDA): Rs3540/- inclusive of GST
Empanelment of Probationary Independent Data Auditors is open to all interested persons to take up Data Auditing.
Benefits: Mentored placement with experienced auditors, discounted training and practice labs, access to sample audit materials, and a pathway to AIDA upon meeting experience and training milestones.
2) Accredited Independent Data Auditor (AIDA): Rs7080/- inclusive of GST
Empanelment of Accredited Independent Auditors is restricted to those who hold relevant certifications in Privacy or Information Security or Law or Chartered Accountancy, or Cost Accountancy or Company Secretary or other approved certifications. (Check for clarification if required). Necessary evidence needs to be provided for confirmation.
Benefits: Inclusion in AIDAI directory, eligibility for Sectorial-focused audit projects, access to audit templates and checklists, discounted FDPPI resources and webinars, and referral support for client engagements.
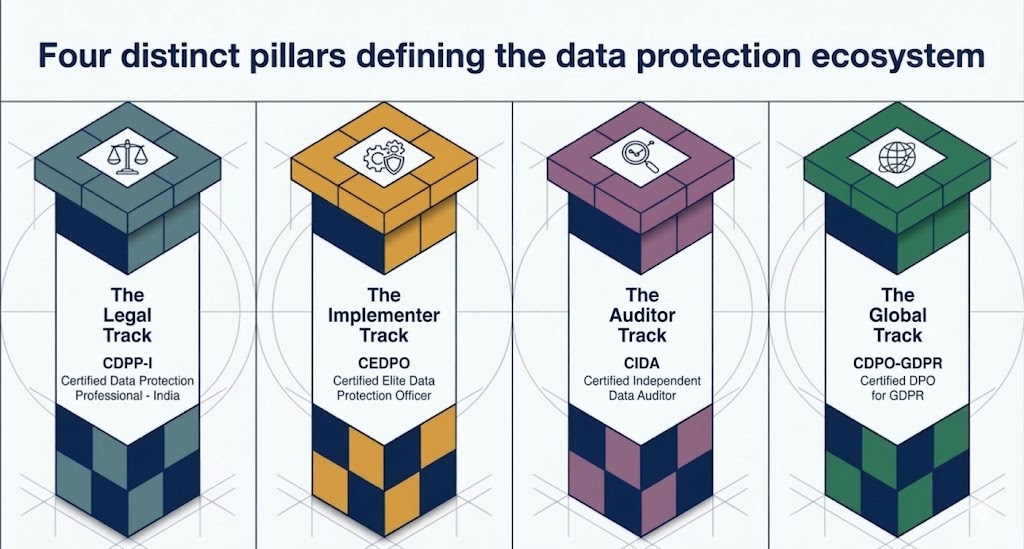
3) Certified Independent Data Auditor (CIDA) : Rs11800/- inclusive of GST
Empanelment of Certified Independent Data Auditors is restricted to those who have passed the CIDA examination of FDPPI.
Benefits: Priority listing for large-scale audit assignments, eligibility to lead multi-auditor engagements, FDPPI endorsement for client proposals, continuing professional development credits, and preferential rates on FDPPI training and certification renewals.
Welcome to Introductory Free Webinar: Saturday, 23rd May 2026 @ 11:00AM to introduce AIDAI, explain the empanelment process, and answer your questions, we are organizing a webinar on Saturday, 23rd May 2026 @ 11:00AM.
The session will cover empanelment criteria, application process, code of conduct, empanelment workflow, and commercial terms. There will be a live Q&A to address role-specific queries for Legal and GST professionals.
Please register to join the webinar using the Zoom link below:
https://us02web.zoom.us/j/88286391275?pwd=wrP6fgGrCWTOVPv9p53RFvo22JgeJo.1
Meeting ID: 882 8639 1275
Passcode: 700473
Time: Saturday, 23rd May 2026 @ 11:00AM
We believe AIDAI will create meaningful professional opportunities and help expand high-quality data protection audit capacity, especially for MSMEs that need practical, affordable compliance support. We look forward to your participation and questions during the webinar.
Warm regards,
Srivatsa. R
Chapter Representative, FDPPI / AIDAI
secretary@aidai.org.in
For more details visit https://aidai.org.in and https://fdppi.in;